As the world becomes increasingly digitized and interconnected, the risks of cyber attacks and data breaches continue to grow. Organizations of all sizes and industries are realizing the need to invest in robust cybersecurity measures to protect their sensitive information from malicious actors. In this fast-paced and ever-evolving landscape, penetration testing, or pentesting, has emerged as a critical discipline in ensuring the security of digital systems.
With the multitude of tools, techniques, and methodologies available to pentesters, it can be overwhelming for aspiring professionals to navigate the path towards expertise. This is where the Pentester Blueprint PDF comes into play. This comprehensive guide provides a roadmap for individuals looking to build a successful career in penetration testing, outlining the essential skills, knowledge areas, and resources necessary to succeed in this demanding field.
The Pentester Blueprint PDF covers a wide range of topics, including network security, web application security, wireless security, reverse engineering, and more. Each topic is explored in detail, providing readers with a solid understanding of the concepts and techniques employed by pentesters in their day-to-day work. Whether you’re a beginner looking to get started in cybersecurity or an experienced professional looking to upskill, this guide is designed to help you progress in your career and stay ahead of the ever-evolving threat landscape.
Pentester Blueprint PDF
A pentester blueprint PDF is a valuable resource for cybersecurity professionals looking to enhance their skills and knowledge in the field of penetration testing. A pentest blueprint PDF provides a comprehensive guide that outlines the methodologies, techniques, and tools used by pentesters to identify and exploit vulnerabilities in computer systems and networks. It serves as a roadmap for aspiring pentesters, helping them develop a structured approach to conducting penetration tests.
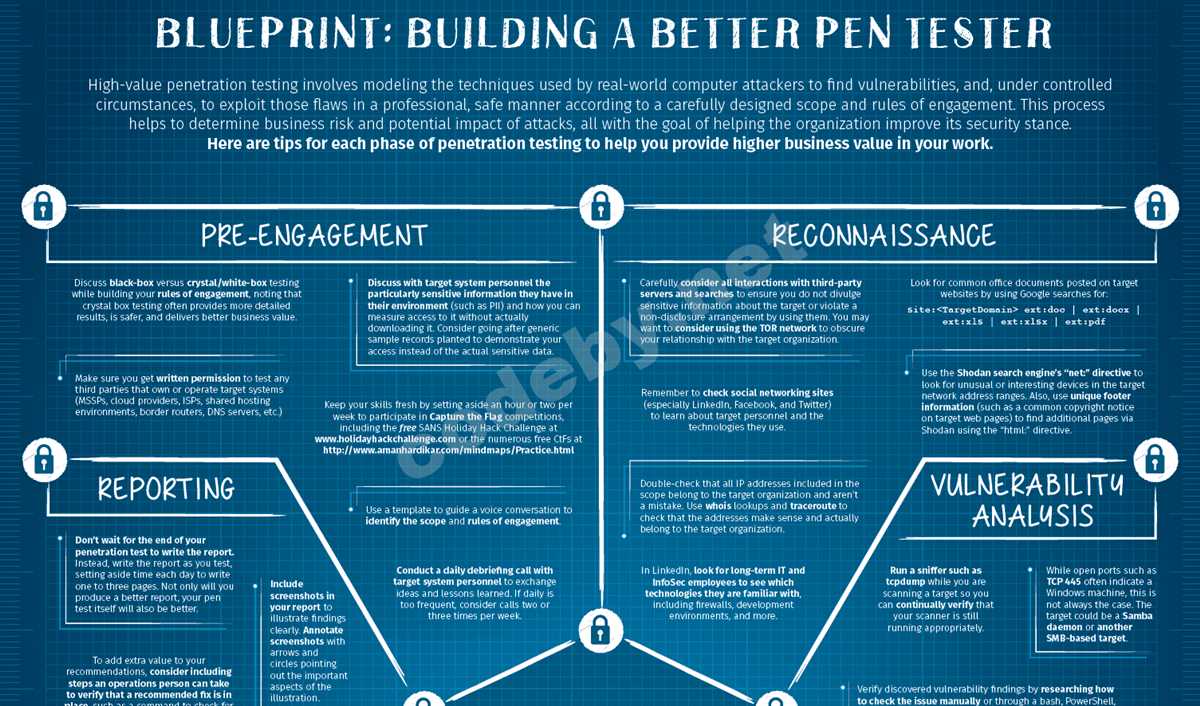
The pentester blueprint PDF typically covers various topics, including reconnaissance, scanning, exploitation, post-exploitation, and reporting. It provides detailed explanations of different attack vectors and their associated countermeasures, allowing pentesters to understand the vulnerabilities and weaknesses of a target system. The blueprint also highlights the importance of ethical hacking and emphasizes the need to obtain proper authorization before conducting any penetration testing activities.
Within the pentester blueprint PDF, you will find recommended tools and techniques for each phase of a penetration test. This includes popular frameworks such as Metasploit, Nmap, Burp Suite, and Wireshark, as well as scripting languages like Python for creating custom exploits. The document may also include best practices and real-world examples that highlight common vulnerabilities and attack scenarios, giving pentesters hands-on experience in identifying and exploiting security weaknesses.
A pentester blueprint PDF is not only useful for individuals seeking to become pentesters, but also for organizations looking to evaluate and enhance their cybersecurity posture. It provides a standardized methodology that can be applied by security teams to proactively identify and mitigate potential vulnerabilities. By following the guidelines outlined in the blueprint, organizations can ensure that their systems and networks are secure against modern threats and attacks.
A pentester blueprint PDF is a valuable resource that empowers cybersecurity professionals with the knowledge and skills needed to effectively identify and exploit vulnerabilities. Whether you are an aspiring pentester or part of a security team, utilizing a pentester blueprint PDF can provide you with a structured approach to conducting penetration tests and enhancing the overall security of computer systems and networks.
What is a Pentester Blueprint?
A Pentester Blueprint is a detailed guide or plan that outlines the steps and processes involved in conducting a penetration test. It serves as a roadmap for ethical hackers, or penetration testers, to systematically identify vulnerabilities and weaknesses in a target system or network. The blueprint provides a structured approach and methodology, ensuring that all necessary areas of the system are assessed and tested.
Typically, a Pentester Blueprint includes various stages and activities, such as reconnaissance, scanning, exploitation, post-exploitation, and reporting. Each stage is carefully planned and executed to gather information, identify potential vulnerabilities, exploit them, and document the findings. The blueprint may also include specific tools and techniques that are commonly used in penetration testing, ensuring that the testers have the necessary resources to perform their tasks effectively and efficiently.
The Pentester Blueprint not only helps testers in performing their tasks, but it also serves as a documentation of the entire penetration testing process. This documentation is important for both internal and external stakeholders, as it provides an overview of the vulnerabilities and risks associated with the target system or network. It also helps organizations in identifying and addressing these vulnerabilities, thereby improving their overall security posture.
Benefits of Using a Pentester Blueprint PDF
Using a pentester blueprint PDF can bring several benefits to professionals in the field of cybersecurity. A pentester blueprint PDF serves as a comprehensive guide that outlines the various steps and processes involved in conducting successful penetration testing. It provides a structured approach to identifying vulnerabilities in systems and applications, allowing pentesters to efficiently assess the security posture of a target.
One of the key benefits of using a pentester blueprint PDF is the time-saving aspect it offers. By following a well-defined roadmap, pentesters can streamline their workflow and ensure that no crucial steps are missed during the assessment process. This saves valuable time and allows pentesters to focus on the actual testing and analysis rather than spending excessive amounts of time on planning and organizing their approach.
The pentester blueprint PDF also acts as a knowledge repository, capturing best practices, tools, and techniques that have been proven effective in the field. It serves as a reference guide, enabling pentesters to quickly access relevant information when needed. This helps to standardize the practices and methodologies followed by pentesters, ensuring consistency and effectiveness across different projects.
Moreover, a pentester blueprint PDF promotes collaboration and knowledge sharing within a team. It can be easily shared among team members, allowing them to align their efforts and work together towards achieving the objectives of the penetration testing project. The blueprint serves as a common reference point, minimizing the chances of miscommunication and enhancing the overall efficiency and effectiveness of the team.
In conclusion, the use of a pentester blueprint PDF brings numerous advantages to professionals in the cybersecurity field. It provides a structured approach, saves time, acts as a knowledge repository, and promotes collaboration within a team. By leveraging these benefits, pentesters can enhance their capabilities and contribute to the overall improvement of the security posture of organizations.
How to Find a Pentester Blueprint PDF
Aspiring and experienced pentesters alike are constantly looking for resources to enhance their skills and knowledge in the field of cybersecurity. One valuable resource that many seek is a pentester blueprint PDF, which provides a comprehensive guide or roadmap for success in this specialization. However, finding an authentic and reliable blueprint can be challenging, considering the vast amount of information available online.
To begin your search for a pentester blueprint PDF, start by consulting trusted sources such as cybersecurity forums, industry blogs, and reputable online communities. These platforms often share valuable resources, including recommended reading materials and study guides, which may include a PDF version of a pentester blueprint. Additionally, professional organizations and certification bodies in the field of cybersecurity, such as EC-Council or Offensive Security, may offer official blueprints or study guides as part of their certification programs.
Another effective approach is to reach out to experienced pentesters or cybersecurity professionals through networking events, conferences, or online platforms like LinkedIn. These individuals may have valuable insights and recommendations on where to find reliable and up-to-date pentester blueprint PDFs. Networking with peers in the cybersecurity industry can not only lead to discovering relevant resources but also foster professional relationships that can be beneficial for future collaboration and knowledge sharing.
When evaluating a potential pentester blueprint PDF, ensure that it covers the essential topics and skills necessary for a successful career in penetration testing. Look for a comprehensive outline that includes areas such as network security, web application security, vulnerability assessment, and various tools and methodologies used in penetration testing. Additionally, consider the reputation of the author or the organization behind the blueprint, as well as any reviews or feedback from other professionals in the field.
Remember that a pentester blueprint PDF should serve as a guide and reference, but practical hands-on experience and continuous learning are equally important. Experimenting with different tools and techniques in a controlled environment, participating in capture the flag (CTF) competitions, and pursuing relevant certifications can further enhance your skills and build a solid foundation in penetration testing.
Key Components of a Pentester Blueprint PDF
When it comes to conducting effective penetration testing, a well-structured blueprint is essential. A pentester blueprint PDF provides a comprehensive and organized guide for conducting penetration tests and ensuring that all necessary steps are followed. In order to create a useful blueprint, there are several key components that should be included:
1. Scope of the Test
Clearly defining the scope of the penetration test is crucial to ensure that the appropriate systems and applications are targeted. The blueprint should specify which assets are in-scope and out-of-scope, as well as any limitations or constraints that should be taken into consideration during the testing process. This helps to streamline the testing efforts and ensures that the objectives of the test are aligned with the goals of the organization.
2. Testing Methodology
The pentester blueprint PDF should outline the testing methodology to be used during the assessment. This includes the different types of tests that will be performed, such as network penetration testing, web application testing, or wireless network testing. It should also specify the tools and techniques that will be employed, ensuring that the pentester has a clear plan of action to follow during the testing process. This helps to maintain consistency and ensures that all relevant areas are thoroughly assessed.
3. Reporting Structure
A well-structured and detailed reporting structure is essential for communicating the findings of the penetration test effectively. The blueprint should specify the format and structure of the final report, including the sections to be included and the level of detail required. It should also outline the timeline for reporting and any specific requirements for remediation or mitigation of vulnerabilities that are identified. This ensures that the pentester has a clear understanding of the expectations and requirements for the final report.
4. Communication Plan
Effective communication is essential throughout the penetration testing process. The blueprint should outline the communication plan, including the individuals or teams that need to be informed of the testing activities, progress updates, and any significant findings or vulnerabilities. It should also specify the preferred method of communication, whether it is through email, meetings, or another form of communication. This helps to ensure that all relevant stakeholders are kept informed and that there is a clear channel of communication between the pentester and the organization.
By including these key components in a pentester blueprint PDF, organizations can ensure that their penetration tests are conducted in a structured and systematic manner. This helps to maximize the effectiveness of the testing process and ensure that all vulnerabilities are identified and addressed.
Tips for Using a Pentester Blueprint PDF effectively
When using a Pentester Blueprint PDF, it’s important to keep a few key tips in mind to ensure that you are maximizing its effectiveness. Here are some tips to help you get the most out of your Pentester Blueprint PDF:
1. Familiarize yourself with the contents
Take some time to thoroughly review the contents of the Pentester Blueprint PDF before diving into any specific tasks. This will give you a good understanding of what to expect and help you plan your approach accordingly.
2. Use it as a reference guide

The Pentester Blueprint PDF should serve as a reference guide rather than a step-by-step tutorial. Use it to gain insights, best practices, and techniques that you may not have otherwise considered.
3. Adapt it to your specific needs
Remember that the Pentester Blueprint PDF is a general guide and may not address all the unique requirements of your particular project or situation. Adapt and customize the techniques and methodologies to fit your specific needs and goals.
4. Take notes and add annotations
While using the Pentester Blueprint PDF, make sure to take notes and add annotations. This will help you capture important insights, brainstorm new ideas, and keep track of any modifications or adjustments you need to make.
5. Seek additional resources
Although the Pentester Blueprint PDF can be a valuable resource, don’t forget to seek additional resources such as online tutorials, forums, and communities for more learning and support. This will enhance your knowledge and provide a broader perspective.
6. Stay updated
Keep in mind that technology and security landscapes constantly evolve. Make it a habit to stay updated with the latest trends, vulnerabilities, tools, and techniques. This will ensure that you are always equipped with the most relevant information and skills.
By following these tips, you can effectively utilize a Pentester Blueprint PDF to enhance your penetration testing skills and achieve more successful and impactful results.
Q&A:
What is a Pentester Blueprint PDF?
A Pentester Blueprint PDF is a document that provides guidance and instructions on how to perform penetration testing effectively. It includes step-by-step methodologies, tools, techniques, and best practices for conducting security assessments.
How can I use a Pentester Blueprint PDF effectively?
To use a Pentester Blueprint PDF effectively, you should read it thoroughly to understand the methodologies and techniques it presents. You can then apply these concepts in real-world scenarios by following the recommended steps and using the suggested tools. It is also essential to keep the document updated and refer back to it regularly for reference and additional guidance.
Where can I find a Pentester Blueprint PDF to use?
Pentester Blueprint PDFs can be found online through various sources. You can search for them on security-related websites, forums, or blogs. Additionally, some pentesting organizations or professionals may offer their blueprints for download on their websites or as part of training courses.